Drone racing is a competitive sport where participants fly small, remote-controlled drones at high speeds through a designated racecourse. It combines the thrill of piloting drones with the excitement of a competitive race. Drone racing has gained popularity in recent years, with organized events, leagues, and championships taking place around the world.
Read MoreCategory: technology
what is game design?
Game design refers to the process of creating the rules, mechanics, interactions, and overall structure of a game. It involves the conceptualization, planning, and implementation of various elements that make up a game, including its objectives, gameplay mechanics, levels, characters, story, visuals, sound, and user experience.
Read More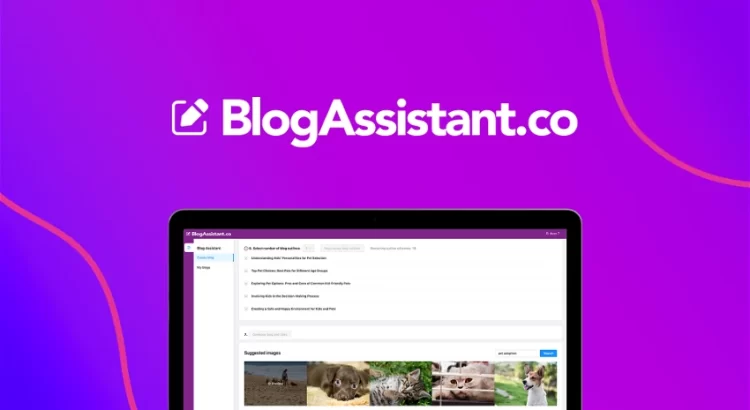
AI-Driven Content Writing & SEO Optimization with BlogAssistant
At BlogAssistant, you can find all the help you require to take your content writing and blog skills up a notch. They have solutions for beginners as well as professional writers so that they can get SEO optimization and digital marketing assistance according to their specific needs. Through AI-generated tools on the platform, they ensure that your content is engaging, optimized for maximum success, and most importantly – properly optimised from an SEO perspective!
Read More
What does PHEV mean?
“PHEV” stands for “Plug-in Hybrid Electric Vehicle.” It refers to a type of hybrid vehicle that combines an internal combustion engine (typically fueled by gasoline or diesel) with an electric motor and a rechargeable battery.
Read MoreWhat is Aerogel
Aerogel is a synthetic porous ultralight material derived from a gel, in which the liquid component for the gel has been replaced with a gas. It is an amazing material with incredible properties like being up to 95% air and able to insulate up to four times better than any other known material.
What is wpl?
WPL stands for “WordPress Property Listing”. It is a popular WordPress plugin used for creating real estate websites and managing property listings. The plugin includes features such as property search, property listings management, front-end property submission, and more. It is widely used by real estate agents, brokers, and property managers.
What does CISA mean?
CISA stands for “Cybersecurity and Infrastructure Security Agency.” CISA is a United States government agency responsible for protecting the nation’s critical infrastructure from cyber threats and physical attacks. The agency was established in November 2018, as part of the Department of Homeland Security (DHS), and is tasked with coordinating with other federal, state, local, and private sector entities to manage and respond to cybersecurity and infrastructure security risks. CISA’s responsibilities include sharing threat intelligence and providing guidance on best practices for cybersecurity and critical infrastructure protection, as well as responding to and investigating cybersecurity incidents and promoting resilience in the face of emerging threats.
What does infosec mean?
Infosec is an abbreviation for “information security,” which refers to the practice of protecting digital information, such as electronic data, systems, and networks, from unauthorized access, use, disclosure, disruption, modification, or destruction. Infosec involves a range of strategies, technologies, and best practices to safeguard data and ensure the confidentiality, integrity, and availability of information. Common infosec measures include access control, authentication, encryption, firewalls, intrusion detection and prevention systems, security assessments, and incident response planning. In today’s world where digital information is a valuable asset, infosec is essential for organizations and individuals to maintain the privacy and security of their information.
What does CVE mean?
In the field of cybersecurity, CVE stands for “Common Vulnerabilities and Exposures”. CVE is a dictionary of publicly known cybersecurity vulnerabilities and exposures that are identified, named and tracked by the CVE program. The purpose of CVE is to provide a standardized naming convention and a centralized database of vulnerabilities found in software and hardware systems. By using CVE identifiers, organizations and security researchers can more easily share information about vulnerabilities and take steps to mitigate the associated risks. The CVE system is maintained by the MITRE Corporation, a nonprofit organization that operates research and development centers for the US government.
What is a sneakernet?
Sneakernet is a term used to describe the practice of physically transporting data files, often on portable storage devices such as USB flash drives or external hard drives, between computers or networks that are not connected to each other. The term “sneakernet” is a play on the term “ethernet”, which is a common computer networking technology.
Read More